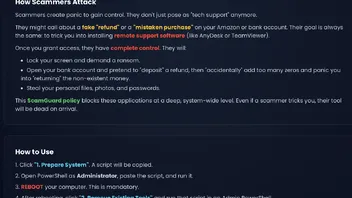
Hawk Eye Safety Net blocks malicious websites and downloads.
Posts by Trident
-
-
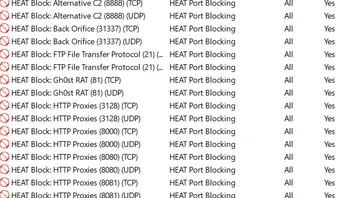
This is an announcement for HEAT:
CrowdStrike Falcon API and Sophos InteliX have been chosen to support threat detection in HEAT.
This is in addition to the proprietary heuristics, static analysis and connection control.
The APIs will further strengthen the protection offered by HEAT and will prepare the product for entry of the premium market.
The APIs will be used based on file origin and other pre-analysed parameters.
Meanwhile, I am also experimenting with API hooking and behavioural monitoring. -
-
-
It’s gonna be a big one.
The architectural design for HEAT has been outlined.
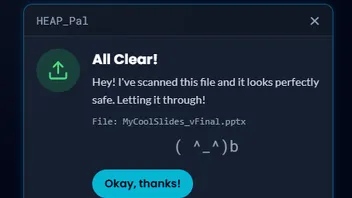
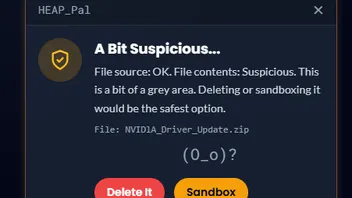
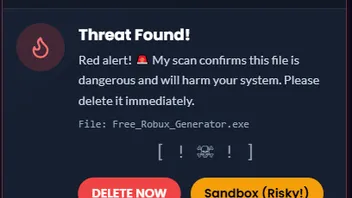
C++ based assembliesBrowser extension passes information about downloads to HEAT. Based on the website and file indicator, HEAT can decide to:
- Leave the file alone. This will be trusted file from a website that is in the bloom list
- Sandbox and monitor once: for the purpose HEAT will come bundled with the open source Sandboxie
- Immediately remove with no monitoring: this will be files with high confidence indicators from websites that are not on the bloom
Continuous Firewall Control (CFC):HEAT will delete all default Firewall rules and will create new rules for applications. The rules however will manage every connection individually. E.g. wuaclt may be allowed to access the Windows Update servers but will not be allowed to access anything else.
What this design requires:+Browser Extension
+ Worker service
+ WPF background process that can display notifications and interact with the user.
Please let me know your thoughts and comments down bellow.
-
-
-
The new logo more closely relates CyberTopix to the Hawk Eye ecosystem of products.
Meanwhile, changes are expected on the official website for HEA—the website will slowly be migrated from in browser transpilation to pre-compiled code.
This means that the website JavaScript will be trimmed by approximately 5 megabytes (for some pages).
The loading times will be shortened (at least halved), which is essential for efficient SEO.
Support pages coming soon, with official forum of the project being CyberTopix.
What do you think of the new logo? -
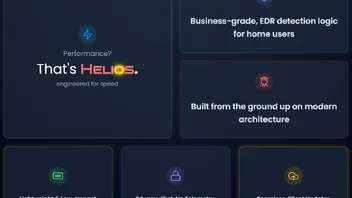
Announcing the future of HEAT (HEAT 2.0).
You spoke and we (or I) listened.
HEAT very soon won’t be a script but will be an executable.
HEAT started as a very small scanning script.
With a bunch of updates, it expanded immensely to a 5K lines of code (very long lines) and a bunch of dependancies.
Over the past few weeks I converted portions of HEAT from PowerShell code to C# (.net 10).
Why .net? Because it allows better access to Windows APIs, which on C++ will need external dependencies and frameworks.
So what is the performance difference?
Memory usage:PowerShell: 1200 mb average
.net: less than 100 mb
Scan time:2.5-3 min average on PowerShell
Seconds on .net
CPU usage:12% on PowerShell
Less than 5% on .net
Size:This is where PowerShell script wins at less than a megabyte
.net: still deciding whether I want portable executable or installer, either way, the total project size will be around 50MB.
How many times the project was refactored:UI:
Rewritten 3 times
From plain javascript to react with in-browser transpiler to precompiled react running on WebView.
Backend:Rewritten 3 times. From monolithic PowerShell to dot sourced, multi-file multi-threaded PowerShell (extremely advanced). Then rewritten to .net.
The backend now dynamically communicates to the UI which is to be expected. 7zip will no longer be needed, it will be replaced by internal SharpZipLib (SharpZipLib.dll).
Heat is developed with love and care and I hope users will love the project as much as I do.
-
Just a clarification, ScamGuard does not rely on Microsoft Defender to work and can be used alongside any antivirus.
-
-
Stay tuned!
ScamGuard will be releasing in the following few days. -
Andy Ful is more than welcome to join.
-
This thread monitors the updates to HEAT.
Although it is called a “tool”, the project has evolved to product.
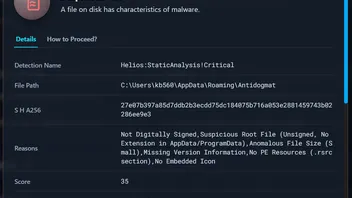
1.25.07This new update brings the following enhancements:
+Performance improvements, especially in static analysis
+Heuristics improvements
+ The rebranding from Orion to Helios is now complete. All detection prefixes have been updated accordingly.
The naming convention remains <engineName>:<threatCategory>!specificInfo -
Morro I think the Eset HIPS with additional hardening is an overkill.
Keep it simple, the HIPS rules already close quite a lot of potential for attacks. -
-
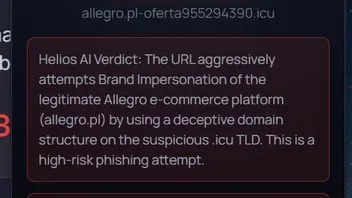
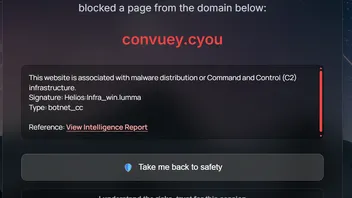
Usually to achieve these warnings and blocks, extensions and AV software add hooks to the browser and potentially, to the pages code.
It takes a lot of know-how as to where exactly the hooks (be it in a page or in the browser memory) are best to be injected, to avoid this condition where the browser and the extension are “racing” who will block the page first.
I’ve also noticed that McAfee works before the native browser features can block the page.This is similar to the file scanning as well, where the minifilter has to be injected at several different places (different altitudes) to ensure files are blocked before the user can open them.
-
Analyse It! is scheduled for a rebrand. Before the rebranding commences, it will be known and referred to as Analyse It!
https://hea-p.com
Analyse It! User Guide
Your comprehensive guide to analyzing suspicious websites and files.
Table of Contents
- Introduction
- Getting Started
- Interface Overview
- Web Test View
- File Test View
- File Analysis Modal Deep Dive
- IoC Manager View
- CADY AI Assistant
- Settings
- Themes
- Troubleshooting (CORS Proxy)
Introduction
Welcome to Analyse It! This platform is designed to streamline the process of analyzing potentially malicious websites and files. It integrates with several leading threat intelligence APIs (VirusTotal, Hybrid Analysis, AbuseIPDB, Google Gemini) to provide comprehensive insights.
Whether you're testing the effectiveness of security solutions, investigating suspicious links, or analyzing malware samples, Analyse It! provides a centralized dashboard to manage your workflow.
Getting Started
Launching the App
When you first open the application, you'll see a welcome screen with an animated background. Click the "Let's Get Started" button to enter the main dashboard.
Initial Setup: API Keys
To unlock the full potential of Analyse It!, you'll need API keys for the integrated services. It's highly recommended to add these right away.
- Click the Menu icon (☰) in the top-left corner.
- Select Settings from the menu.
- Navigate to the API & Security tab.
- Enter your API keys for:
- Gemini API Key: For AI-powered analysis and CADY assistant. Get one from Google AI Studio.
- VirusTotal API Key: For URL scanning, file hash lookups, reputation checks. Requires a free VirusTotal account.
- AbuseIPDB API Key: For IP address reputation checks. Requires a free AbuseIPDB account.
- Hybrid Analysis API Key: For deeper file analysis (requires SHA256 hashes). Requires a free Hybrid Analysis account.
- API keys are stored in your browser's sessionStorage for security and are not persisted between sessions unless you use the State Management export/import feature.
- Consider setting up the Secure Mode with a Cloudflare Worker for enhanced privacy (see Settings section).
While the app can function without API keys, features like scanning, AI analysis, and reputation checks will be unavailable.
Interface Overview
The main interface consists of several key areas:
- Header: Displays the Menu button, the current Product Name (customizable in Settings), and context-specific action buttons (like "Scan URLs").
- Menu (☰): Slides out from the left, allowing navigation between the main views (Web Test, File Test, IoC Manager), opening Settings, launching CADY, and changing themes.
- Main Content Area: Displays the content for the currently selected view.
- Interactive Background: A dynamic, animated background (can be disabled in Settings for performance).
- Modals: Pop-up windows for detailed views (like URL testing, file analysis, settings, AI analysis).
- Toasts: Temporary notification messages appearing at the bottom-center of the screen.
Web Test View
This is the default view, designed for testing web filtering effectiveness or analyzing lists of URLs.
Adding URLs
- Open the Settings panel (Menu > Settings).
- Go to the Website Parsing tab.
- Paste your list of URLs (one per line) into the text area.
- Select the category for these URLs (Phishing or Malware).
- Click "Add URLs".
Understanding the Dashboard
- Stat Cards: At the top, you'll see key statistics: Total URLs, Tested URLs (Blocked + Missed), and Effectiveness %.
- Calculate & Analyze: This button calculates the effectiveness score based on tested URLs and uses the Gemini API (if configured) to generate an AI commentary on the results.
- Filter Controls: Buttons below the stats allow you to filter the displayed URLs by their status (All, Untested, Scanning, Scanned, Blocked, Missed, Dead).
- URL Grid: Displays cards for each added URL, showing its type, URL (truncated), and current status badge.
Manual Testing & Status Updates
- Click on any URL card in the grid.
- A modal window will appear showing the full URL.
- Click "Open in New Tab" to test the URL against your security product.
- After observing the result (blocked page, malicious content loaded, site unavailable), return to the modal.
- Click the appropriate button (Blocked, Missed, or Dead Link) to update the URL's status.
- The modal closes automatically.
VirusTotal Scanning
- Ensure your VirusTotal API Key is added in Settings.
- Click the "Scan URLs" button in the header.
- The app will queue all URLs currently marked as 'Untested' and begin submitting them to VirusTotal (respecting API rate limits).
- The status badge on URL cards will update to 'Scanning...'.
- After a short delay (approx. 15-20 seconds per URL), the status will change to 'Scanned', and the number of malicious detections found by VT will appear in parentheses (e.g., "Scanned (5)").
- Clicking a 'Scanned' URL card will show details about which VT engines flagged it as malicious.
- You can configure the minimum number of VT detections required to automatically flag a URL as malicious in Settings > VirusTotal > URL Detection Threshold (this only affects the display, not the Blocked/Missed status).
AI Analysis
After manually testing some URLs (updating their status to Blocked/Missed/Dead), click the "Calculate & Analyze"button. This provides an effectiveness score and, if the Gemini API key is configured, an AI-generated summary of the test results.
File Test View
This view allows you to analyze files using their cryptographic hashes (MD5, SHA1, SHA256) or by uploading the file directly.
Submitting Files
You have two options:
- By Hash: Paste an MD5, SHA1, or SHA256 hash into the input field and click the Search icon or press Enter.
- By Upload:
- Drag and drop a file onto the designated drop zone.
- Alternatively, click the drop zone to browse and select a file.
- The file is hashed locally in your browser using the SHA-256 algorithm. The file content itself is not sent unless you explicitly upload it to VirusTotal/Hybrid Analysis (requires API keys).
- After hashing, the SHA256 hash automatically populates the input field.
- If API keys are configured, the app will attempt to upload the file to VirusTotal and/or Hybrid Analysis for scanning. Upload progress is shown briefly.
- Finally, the app performs a lookup using the calculated hash.
Analysis Context (Sample Source)
Before the analysis begins, you'll be prompted to specify the file's origin (Email, Untrusted Website, Trusted Website, Other/Unknown). This context helps the AI tailor its behavioral risk scoring ('Aggressive' vs. 'Standard' stance).
Understanding Results
Once the lookup is complete (using VT and/or HA APIs if keys are provided), a result card appears:
- Displays basic file info (type, primary name, hash).
- Shows the VirusTotal detection score (malicious engines / total engines).
- Shows the Hybrid Analysis verdict (Malicious, Suspicious, Safe) if available.
- Clicking this card opens the detailed File Analysis Modal.
File Analysis Modal Deep Dive
This modal provides a comprehensive view of the analyzed file across several tabs.
Tabs Overview:
- Threat Factor (OTS): (Requires VT data) Calculates an Overall Threat Score based on multiple factors: sample origin, timestamp anomalies, engine consensus (VT/HA), and AI behavioral scoring. Provides a quick risk assessment.
- Summary: (Requires VT data) Shows basic file details (name, type, size, first seen) and hashes (MD5, SHA1, SHA256). Allows adding hashes to the IoC Manager. Displays the selected Analysis Stance (Aggressive/Standard).
- Detections: (Requires VT data) Lists all engines that detected the file as malicious, along with their specific detection names. Includes the VT Interpretation Heuristic score and commentary if enabled in Settings.
- Behaviour: (Requires VT data) Displays detailed sandbox behavioral data from VirusTotal, grouped by category (Commands, Network, Files Dropped/Opened/Written/Deleted, Registry Set/Deleted). You can add observed indicators (IPs, domains, hashes, paths, keys) directly to the IoC Manager. Also shows the AI Behavioural Threat Assessment score and verdict if enabled and calculated.
- Hybrid Analysis: (Requires HA data) Shows the HA verdict, threat score, MITRE ATT&CK techniques observed by HA, and contacted hosts/domains. Allows checking reputation and adding IoCs.
- AI Analysis: (Requires Gemini API Key & VT/HA data) Allows you to request an AI-generated analysis of the file based on the available VT/HA reports. You can choose the desired response length (Concise, Balanced, Expert).
- ATT&CK Matrix: (Requires Gemini API Key & VT Behaviour data) Generates a MITRE ATT&CK matrix by mapping observed sandbox behaviours to specific tactics and techniques using AI. Hover over techniques for details and click to view them on the official MITRE website.
Exporting Reports
Click the Download icon in the modal header to export a summary of the analysis findings (including details from most tabs) as a PDF document.
IoC Manager View
This view acts as a central repository for Indicators of Compromise gathered during your analyses.
Adding IoCs
- Manually: Enter the IoC value (e.g., `evil.com`, `1.2.3.4`, a file hash), select its type (Domain, IP, Hash, URL, etc.), and click "Add".
- From File Analysis: Use the '+' icon next to indicators in the File Analysis Modal (Summary, Behaviour, Hybrid Analysis tabs) to add them directly. The 'Source' column will show the SHA256 hash of the file from which the IoC originated.
Managing IoCs
- Viewing: The table displays the IoC value, type, source (manual or file hash), and the date added.
- Checking Reputation: For IP addresses and Domains, click the shield icon (🛡️) to check their reputation using AbuseIPDB (for IPs) or VirusTotal (for Domains), provided the respective API keys are configured. Results appear in a tooltip.
- Removing: Click the red 'X' icon to remove an IoC from the list.
Exporting IoCs
Use the buttons at the bottom ("Export as CSV", "Export as JSON") to download your collected IoCs for use in other security tools or reports.
CADY AI Assistant
CADY (Cyber Analysis & Defense AI) is your conversational AI partner, powered by Google Gemini.
Accessing CADY
- Open the Menu (☰).
- Click "Talk to CADY".
Using CADY
- Context-Aware: If you open CADY while viewing a file analysis (File Test view with results loaded), CADY automatically receives the VT and HA reports as context.
- Ask Questions: Type your questions about the current file analysis (e.g., "Summarize the malware's main goal", "What does the registry key modification signify?", "Generate detection rules for this file") into the input field and press Enter or click Send.
- Response Length: Use the toggles (Short, Medium, Expert) to control the detail level of CADY's responses.
- Requirements: CADY requires a valid Gemini API Key configured in Settings.
Settings
The Settings panel allows you to configure API keys, customize behavior, and manage application data.
Tabs Overview:
- Website Parsing:
- Product Name: Customize the name displayed in the header and used in AI analysis prompts.
- Parse & Add URLs: Add lists of URLs and categorize them.
- Danger Zone: Clear all URLs currently loaded in the Web Test view (irreversible).
- API & Security:
- Enter API keys for Gemini, VirusTotal, AbuseIPDB, and Hybrid Analysis.
- Secure Mode: Configure a Cloudflare Worker URL to proxy API calls, avoiding the need for the public CORS proxy and keeping API keys more secure (requires setting up the provided worker code in your Cloudflare account).
- Public CORS Proxy: Provides a link to activate the `cors-anywhere` public proxy if not using Secure Mode (required for most API calls to function due to browser security restrictions).
- VirusTotal:
- URL Detection Threshold: Set the minimum VT detections needed to highlight a URL score in the modal.
- Deduplicate Detections: (File Analysis) Hides similar detection names from lower-tier AV engines for clarity.
- Enable Interpretation Heuristic: (File Analysis) Calculates and shows a weighted VT threat score and commentary.
- AI Behaviour:
- Enable AI Behaviour Scoring: (File Analysis) Automatically uses Gemini to analyze sandbox behavior and provide a risk score/verdict.
- Default AI Analysis Level: Sets the default detail (Concise, Balanced, Expert) for AI analyses requested automatically or manually.
- Performance:
- Enable Background Animations: Toggle the interactive background animations on/off. Disabling may improve performance on less powerful devices.
- State Management:
- Export State: Saves your current settings (including API keys stored in sessionStorage) to a JSON file. Useful for backups or transferring settings.
- Import State: Loads settings from a previously exported JSON file.
Themes
You can change the visual appearance of the application.
- Open the Menu (☰).
- At the bottom of the menu, under the "Themes" heading, click on the desired theme (Slate, Light, Cyberpunk).
- The interface will update instantly. Your theme preference is saved locally.
Troubleshooting (CORS Proxy)
Modern web browsers have security restrictions (CORS) that prevent web pages from directly calling APIs on different domains (like VirusTotal, Gemini, etc.).
Solutions:
- Recommended: Secure Mode (Cloudflare Worker):
- Go to Settings > API & Security.
- Copy the provided Worker script.
- Deploy it to your own Cloudflare account. Instructions are widely available on the Cloudflare website.
- Paste your unique Worker URL (e.g., `https://my-worker.example.workers.dev`) into the "Cloudflare Worker URL" field in the settings.
- Important: You must also add your API keys within the `API_KEYS` constant directly in the Cloudflare Worker code for this method to work securely. The keys entered in the app's settings panel are not used when a Worker URL is specified.
- This method routes API calls through your own proxy, offering better privacy and reliability.
- Alternative: Public CORS Proxy:
- Go to Settings > API & Security.
- Click the "Activate Proxy" button under "Public CORS Proxy".
- This opens the `cors-anywhere` demo page in a new tab. Click the button on that page to request temporary access for your browser.
- Return to the Analyse It! tab. API calls should now work for your current browser session.
- This method uses a free, public proxy which may have limitations or reliability issues. You might need to reactivate it periodically.
If API calls (like VT scanning or AI analysis) fail with "Forbidden" or network errors, it's almost always a CORS issue. Ensure you have either configured Secure Mode correctly or activated the public proxy.
© Analyse It! - Happy Analyzing!
-
The Orion Remediation Tool is scheduled for a rebranding. Until the rebranding commences it will be known and referred to "Orion Standalone Remediation Tool" or "Orion Malware Cleaner".
Orion Remediation Tool
A comprehensive user guide for the standalone threat remediation script.
Thank you for choosing Orion Malware Cleaner. It's important to understand that this is not an antivirus replacement with real-time protection. Instead, it is a powerful, on-demand threat investigation and remediation toolkit designed for knowledgeable users to hunt for and remove active and dormant threats.
This guide will walk you through the entire process, from launching the script to understanding its findings and taking action. The tool is designed to be powerful, but its effectiveness relies on informed decisions from you, the operator.
The Boring Stuff (EULA)
Use at Your Own Risk. This is a powerful tool that makes significant changes to your system, including deleting files and modifying the registry. By using this tool, you acknowledge that you are doing so at your own risk. The creators are not liable for any data loss, system instability, or other damages that may result from its use. It is strongly recommended that you back up any critical data before running a scan and performing remediation.
Quick Navigation
- Step 1: Preparation & Execution
- Step 2: Choosing Your Scan Level
- Step 3: Deconstructing the Report
- Live Process Monitor
- Memory Anomaly Detections
- Live Network Connections
- Suspicious Files & Scripts
- Dual-Use & Remote Access Tools
- Suspicious Persistence Mechanisms
- Abused / Vulnerable Driver Detections
- Potentially Unwanted Programs (PUPs)
- System Tampering & Policy Changes
- CPR Toolbox (Clean, Repair, Optimize, Harden)
- System Information
- Step 4: The Remediation Workflow
- Step 5: Post-Remediation
Step 1: Preparation & Execution
Before you even think about running a scan, a few preparatory steps are essential for the best results.
Close All Applications! Before initiating a scan, save your work and close all open programs (web browsers, documents, games, etc.). This does two critical things:
1. It prevents applications from locking files that the script may need to scan or remove.
2. It gives the script a cleaner snapshot of your system's baseline activity, making it easier to spot anomalies.Running as Administrator
The script needs deep access to the system to inspect processes, check system files, and modify the registry. It MUST be run with Administrator privileges.
Execution Policy Bypass (Crucial!)
Windows has a security feature called "Execution Policy" that prevents PowerShell scripts from running by default. To run Orion, you must bypass this policy for this single execution. This does not permanently change your system's security settings.
- Open the Start Menu and type PowerShell.
- Right-click on "Windows PowerShell" and select "Run as administrator".
- In the blue PowerShell window, first navigate to the directory where you saved the script. For example: cd C:\Users\YourUser\Desktop\Orion
- Now, execute the script using the bypass flag. Assuming your script is named sa.ps1, the command is:
PowerShell.exe -ExecutionPolicy Bypass -File .\sa.ps1 - Press Enter. The Orion menu should now appear.
Prerequisites & Automation
The script's capabilities are enhanced by two external tools. The script will automatically search for them in its `modules` subfolder and in common installation paths.
- 7-Zip: If 7-Zip is found, the script enables Quarantine mode. Instead of permanently deleting malicious files, it moves them into a password-protected zip archive. This is the safest option. Without 7-Zip, the script will fall back to permanent deletion.
- Sysinternals Handle: This utility allows the script to identify and terminate processes that have a "lock" on a malicious file, enabling its removal. Without it, some locked files might require a system reboot to be deleted.
Log & Quarantine Location
All operational output, detailed text logs, and quarantine archives are stored in a dedicated folder for easy review: C:\Users\YourUsername\Documents\Orion_Logs\
Step 2: Choosing Your Scan Level
Orion offers three distinct scan levels, allowing you to tailor the depth and duration of the analysis to your needs. Before the menu appears, the script will quickly check the status of its Dynamic Cloud Intelligence (DCI) feeds and download updates if necessary.
[10] Gentle Scan
The fastest scan, designed to find live, active threats. It's a quick health check on what's currently happening on your system.
- Scans running processes for anomalies.
- Inspects loaded modules (DLLs).
- Runs the live network monitor to watch for suspicious outbound connections.
[20] Elevated Scan
A more thorough investigation that includes everything from the Gentle scan, plus a hunt for dormant or persistent threats.
- Scans high-risk folders (Downloads, Temp, etc.) for suspicious files.
- Checks for common persistence mechanisms (e.g., Run Keys, Scheduled Tasks) that malware uses to restart itself.
[30] Aggressive Scan
The most comprehensive analysis. This is a deep-dive that uses multiple engines to inspect every corner of the system for threats, policy violations, and unwanted software.
- Includes all previous checks.
- Activates the Multi-Engine Static Analysis to look *inside* files for malicious characteristics.
- Hunts for Potentially Unwanted Programs (PUPs), vulnerable drivers, and system tampering (e.g., disabled Task Manager).
Step 3: Deconstructing the Report
After the scan, the HTML report is your command center. Findings are grouped into categories, presented as collapsible "accordions". Understanding what each category represents is crucial for accurate remediation.
Built-in Safety and Accuracy! Orion is designed to be both powerful and safe. It includes a Stability Control System to prevent removal of critical Microsoft files, and a Relationship Analysis Engine to intelligently reduce false positives on legitimate third-party software.
Live Process Monitor
This is a snapshot of all processes running on your system at the time of the scan. It is provided for informational and investigative purposes, allowing you to see which processes have network connections, if they are digitally signed, and if they have a visible window.
Memory Anomaly Detections
This category flags suspicious behavior happening in your computer's memory right now. These are active threats that require immediate attention.
What you'll find here:
LOLBin Abuse: "Living-off-the-Land Binaries" are legitimate Windows tools (like powershell.exe) being used maliciously. Orion detects this when they're launched by an unusual parent process (e.g., Word) or with suspicious command-line arguments.
Process Masquerading: A malicious process naming itself after a critical Windows process, like svchost.exe, but running from the wrong location (e.g., a Temp folder instead of C:\Windows\System32).
Process Injection: A legitimate process (like explorer.exe) has loaded an unsigned DLL from a suspicious, user-writable location. This is a classic malware hiding technique.
Live Network Connections
This accordion shows you which non-browser programs are communicating with the internet. It leverages both heuristics and Dynamic Cloud Intelligence (DCI)—a live threat feed of known malicious IPs and domains—to spot hidden C2 channels.
What you'll find here:
Botnet/C2 Detections: High-confidence alerts where a connection matches an entry in the DCI database or a strong heuristic, like a process connecting to an abused service (Discord CDN, Pastebin, Ngrok), a high-entropy domain (suggesting DGA malware), or directly to an IP address without resolving a domain name.
Connection Info: Informational entries showing normal background activity. Review them for context, but they usually don't require action.
Suspicious Files & Scripts
This section is about potentially malicious files lying dormant on your hard drive. These might be droppers, payloads, or malicious scripts waiting to be executed.
What you'll find here:
Static Analysis Detections: Files flagged by looking inside them for suspicious indicators: high entropy (packed/encrypted), missing or fake version information, anti-analysis strings (like `VMWare`), suspicious imported functions, and more.
Relationship Analysis: For files that look suspicious but have some legitimate properties, this engine provides a "Confidence" score. It checks for other signed files from the same software vendor nearby, helping to distinguish a legitimate installer component from a standalone threat.
Suspicious Scripts/LNK/PDF: Scripts (.js, .vbs) with heavy obfuscation, shortcut files (.lnk) that point to malicious commands, and PDFs with active content keywords are flagged here.
Dual-Use & Remote Access Tools
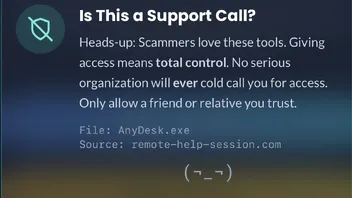
This category lists legitimate software that, while useful for IT professionals, is the primary tool used by attackers and tech support scammers to gain control of a victim's computer.
What you'll find here:
Programs like AnyDesk, TeamViewer, LogMeIn, etc. If you did not explicitly ask a known, trusted IT contact to install this, it should be removed immediately.
Suspicious Persistence Mechanisms
Persistence is how malware survives a reboot. This category is one of the most critical, as it finds the hooks that malware embeds into the system to ensure it runs again every time you start your computer.
What you'll find here:
The script checks all the common hiding spots: Registry Run Keys, Scheduled Tasks, Windows Services, Startup Folders, and more. Finding an unsigned or strangely located program here confirms that the machine is compromised.
Abused / Vulnerable Driver Detections
This category flags the presence of legitimate, signed kernel drivers that are known to contain vulnerabilities. Attackers can abuse these drivers to disable security software or load their own malicious code into the kernel.
What you'll find here:
The script maintains a list of known-vulnerable drivers (e.g., dbk64.sys, gmer.sys). Finding one of these on your system is a high-risk indicator. Unless you have a specific, known reason for having this driver, it should be removed.
Potentially Unwanted Programs (PUPs)
PUPs are not viruses, but they are "junkware" that often comes bundled with other software. They can degrade performance, inject ads, and compromise your privacy.
What you'll find here:
Adware, browser toolbars, and "scareware" system cleaners. Generally, anything found here can be safely removed.
System Tampering & Policy Changes
This section detects when malware has deliberately weakened your system's security settings to make its job easier or to prevent you from fighting back.
What you'll find here:
Common findings include the Task Manager being disabled, Windows Defender exclusions being added for the malware's folder, or the HOSTS file being modified to block you from accessing security websites.
CPR Toolbox (Clean, Repair, Optimize, Harden)
This is a special category containing a suite of proactive tools for system maintenance, hardening, and optimization. These are optional actions you can take to improve your system's health and security posture.
Clean
Actions to remove clutter like temporary files, the Recycle Bin, and old Windows Update caches.
Repair
Tools to verify and repair the integrity of core system files using System File Checker (SFC) and DISM.
Optimize
Actions to improve performance, like running drive optimizers (Defrag/TRIM) and managing startup programs.
Harden
Actions to reduce your system's "attack surface" by enabling advanced Windows Defender features (PUP Protection, ASR Rules) and blocking commonly abused tools from accessing the internet.
System Information
An informational section at the bottom of the report that provides a detailed summary of your computer's operating system, hardware, network configuration, and a list of all installed software for your reference.
Step 4: The Remediation Workflow
Once you have reviewed the findings, you can instruct the script on what actions to take. This is a deliberate, two-step process to prevent accidental changes. Orion also includes several automated remediation enhancements.
Advanced Remediation Features
Chain Remediation: If you select a persistence item (like a Run Key), Orion automatically finds and selects the malicious file it points to for removal.
Correlational Cleanup: After removing a file, Orion scans the same folder for related malware artifacts (like `.dat` or `.zip` files) and removes them. It will also delete the parent folder if it's left empty.
Orphaned Shortcut Removal: Any shortcuts pointing to a file you've selected for remediation will also be automatically removed from the desktop and start menu.
Firewall Rules: In the details modal for any network detection, you have the option to create a Windows Firewall rule to block that specific process or destination IP address from making outbound connections.
- Select Items for RemediationIn the HTML report, go through each category and place a checkmark next to every item you wish to remove or fix. You can use the "select all" checkbox at the top of each table.
- Generate the Remediation FileAfter making your selections, click the orange Generate Remediation File button at the top of the report. This will download a JSON file (e.g., Orion_Remediation_List_....json) to your computer's Downloadsfolder. Do not change the name of this file.
- Confirm in PowerShellGo back to the PowerShell window where the script is waiting. It will now prompt you to "Press any key after you have generated the remediation file". Press any key.
- Execute RemediationThe script will automatically find the JSON file, read your selections, and begin taking action. You will see its progress in the PowerShell window as it quarantines files, removes registry keys, and creates firewall rules.
Step 5: Post-Remediation
After the remediation actions are complete, the script will provide a final summary.
- Summary of Actions: A list of all actions taken will be displayed in the console.
- Quarantine Archive: If quarantine was enabled, it will tell you the path to the password-protected zip file. The password is always infected.
- Reboot Required: If the script was unable to remove a locked file, it will schedule it for deletion on the next reboot. If you see this message, it is critical that you restart your computer to complete the cleanup.
This concludes the manual. Stay vigilant, and happy hunting!
-
Hello,
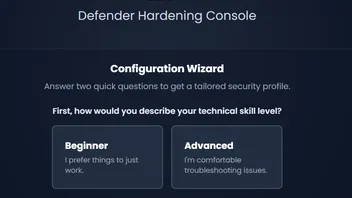
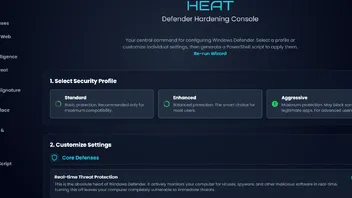
I am excited to announce the official release of Defender Hardening Console (part of HEAP).https://harden.hea-p.com
The Hawk Eye Analysis Platform which I am working on is a set of tools for malware analysis and cleanup.
The Defender Hardening Console takes a proactive stance by hardening the built-in Windows security in a user-fiendly way.
No tools/downloads are required, the project generates PowerShell code which simply needs to be copy/pasted per the instructions.
Special care has been taken for any hardening to not be overdone.
The online console offers the following benefits:
-Enable hidden Microsoft Defender features which bring it on par with the big dogs
-Learn more about the built-in security
-Harden the antivirus and firewall, all in one go.
-Block frequently exploited tools from establishing network connections
-Block common ports used and abused by malware
What does the future hold for this project?
-I've obtained a large set of bot/botnet information, I will use AI to study it and better block ports
-UI improvements (I have obsession with UIs)
-Quick cleanup - Orion Malware Cleaner (which will now be renamed to Hawk Eye Analysis Tool) proved that it is possible to effectively run heuristics in PowerShell.
Very basic cleanup of several locations Defender will not take care of will be added to the console and to the copy/pasted script.
-Standalone firewall hardening compatible with third-party AVs based on Windows Filtering Platform
The script generated has been tested on Windows 11 with Microsoft Defender and Defender Firewall enabled and with latest updates installed.